Network security has changed a lot in recent years, and simple tools no longer offer full protection. Firewalls and passwords are still used by many businesses, and they are frequently compromised by the attackers. Due to that, organizations are now interested in smarter systems, which have a capability of monitoring and controlling the traffic in real-time. Exploring IDS vs IPS, you will be able to figure out how the current security layers combine in detection and prevention of threats. The roles of both systems are not the same; nevertheless, in practical situations, they complement each other. That is why it is possible to develop a more effective, more stable network environment by learning about the way they operate.
Moreover, a layered approach (in which visibility and control have equal importance) is now used in many companies in 2026. Efforts should not be limited to the use of one tool due to the increasing sophistication of threats. This is why knowing about IDS and IPS becomes essential to the IT teams, startups, and even expanding companies. This article is simple but easy to understand with an elaborate explanation of every concept. You will also get illustrations, comparisons, and practical applications that will enable you to link theory to practice.
IDS vs IPS: Understanding Intrusion Detection System Basics
An Intrusion Detection System plays a vital role in monitoring network traffic and identifying suspicious behavior. It stays active, monitoring packet of data traveling over the network and compares them to known patterns of threats. Consequently, it assists security teams to have a clue of what is happening behind the scenes. Besides, threats are not blocked by IDS. Rather, it notifies the administrators of the occurrence of something suspicious. Due to this, teams will be able to investigate the matter and act on the alert. This solution enhances transparency but also enables making better decisions.
In practice IDS does not disrupt traffic and works without any sound. Consequently, companies would want to utilize it when they wish to gain insights on the trends and then impose rigid regulations. It also aids in detection of concealed threats, which are not usually detected. Just to give one example, when an employee tries to make several unsuccessful logins, IDS is able to detect that pattern in no time. It will then give an alert to allow the security personnel to take action before things become worse.
IDS vs IPS: How Intrusion Detection Systems Analyze Traffic
IDS engages sophisticated methods to analyze the network traffic and identify threats. It is also based on behavioral analysis as well as predefined signatures to spot risks. It is due to this that it is able to identify not only known threats, but also unknown threats.
Originally, signature-based detection is used in comparison between entering traffic and a library of previously detected attack signatures. This technique is rapid and can detect frequent threats without any difficulties. But it can fail to detect emerging forms of attacks that fail to comply with the current patterns.
Secondly, anomaly-based detection learns the normal behavior of the user and identifies abnormalities. As an example, when a user accesses large amounts of data unexpectedly at the end of the day (that is, soon before bedtime), the system raises an alarm. Thus, this approach offers more insights into abnormal activities.
Moreover, the IDS uses a combination of both techniques to enhance accuracy. This combination makes sure that even when attackers attempt to masquerade their actions, the system will be able to detect any threats.
Detection Methods Overview:
| Detection Type | Working Principle | Advantage | Limitation |
| Signature-Based | Matches known patterns | Fast detection | Misses new threats |
| Anomaly-Based | Detects unusual behavior | Identifies unknown attacks | May create false alerts |
Because of these methods, IDS becomes a strong monitoring tool that supports proactive security planning.
IDS vs IPS: Exploring Intrusion Prevention System Functionality
An Intrusion Prevention System extends security to a greater level as it actively prevents threats. It is also able to scan traffic in real time, unlike IPS, which is placed inline in the network traffic. Thus, it can avert malicious behavior prior to accessing the system. IPS is not only capable of detecting threats but also prevents them in real-time using its rules. This is why it is one of the most useful instruments of the organizations that require protection on the spot. It also lessens paperwork and therefore time and energy is saved as well as manual intervention.
IPS is favored by many companies, as it provides autonomous responses. To take a case, the system will block a source in case it identifies a suspicious traffic. Consequently, it thwarts damage before it takes place. Besides, IPS assists in preserving the integrity of the systems since it filters harmful data. It guarantees the network only gets through friendly and permissible traffic.
IDS vs IPS: How IPS Detects and Stops Threats Instantly
IPS operates on the basis of constantly examining traffic and implementing preset rules, on the network. It relies on IDS techniques of detection but includes a response layer which responds immediately. Due to this reason, it is able to deal with threats more quickly than manual. Where the system finds some malicious behavior, it blocks or alters the traffic immediately. Examples of this include dropping malicious packets or shutting down of suspicious connections. Hence it is a real-time defense mechanism.
IPS would be very useful in real-world situations when the attack is automated like the botnet. It averts such threats in a fraction of a second, thus implying that they cannot propagate any more. Additionally, IPS assists organizations in autonomy in enforcing security policies. It makes sure that every activity in the network is governed by stipulated rules even without having to closely monitor the activities.
IDS vs IPS: Comparing Network Security Roles and Performance
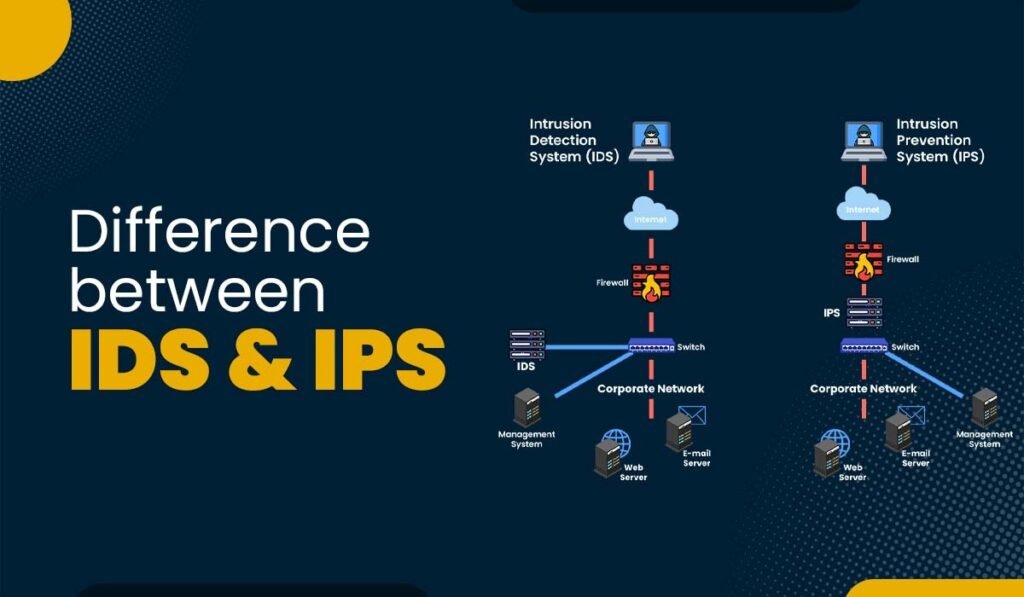
In the comparison made between IDS vs IPS, the biggest difference between the two lies in their method of dealing with threats. IDS is detection-oriented whereas, IPS is prevention-oriented. As such, there are distinct roles of both systems in a network. IDS works without affecting traffic and monitors the information. Due to this it does not have an impact on network performance. On the one hand, IPS acts in the flow of traffic and actively regulates the movement of data.
Response time is also affected by this difference. IDS relies on human intervention as opposed to IPS, which responds immediately. In turn, IPS is faster in protection particularly in the high-risk setting. Nevertheless, IPS can occasionally block out legitimate traffic unless rules are not set accordingly. As such, organisations should be keen to strike a balance between security and usability.
IDS vs IPS Comparison:
| Feature | IDS | IPS |
| Function | Detection | Prevention |
| Placement | Out-of-band | Inline |
| Response Time | Manual | Real-time |
| Risk Level | Low disruption | Possible blocking errors |
| Purpose | Visibility | Control |
This comparison clearly shows how both systems contribute differently to network security.
IDS vs IPS: Shared Features in Modern Cybersecurity Systems
IDS and IPS are considered to be different, but share some common features. Both of them scan network traffic on a continuous basis and have signature databases. Thus, they cooperate in the process of detecting threats. Moreover, both tools produce comprehensive logs, with the assistance of which incidents may be analyzed. These logs can ensure that teams look into past activities and enhance security measures. Due to this, they aid in the process of detection and investigation.
Further, automation is an important factor in the two systems. They are also run without manual checks and this decreases workloads among IT teams. This renders them applicable in both small and big organizations. Current configurations are adopting a number of solutions that integrate IDS and IPS into one platform. This integration eases the management and enhances efficiency.
IDS vs IPS: Practical Limitations and Challenges in Use
IDS and IPS, despite having their advantages, have limitations. Becoming aware of these challenges assists organizations to employ them better. False positives, i. e. a normal activity pass as suspicious, are one of them. An example is a software update that can cause an alert as it will alter traffic patterns. Thus, teams should make changes to settings in systems.
The other issue is with encrypted traffic. As data is encrypted, systems might not be able to comprehend its contents wholly. Consequently, there is a possibility of some threats going undetected. Also, the two systems should regularly be updated to be effective. They might not be able to identify new threats without updated signature databases. Thus, maintenance becomes an essential element of utilization of these tools.
IDS vs IPS: Is It Necessary to Deploy Both Together?
Many organizations wonder whether they should use both IDS and IPS. This will be determined by their security requirements and capabilities. But the majority of the modern configurations have the advantage of integrating both systems. The first step in using IDS is to have the teams familiar with how the network behaves. After perfecting alerts, they can have IPS auto-respond. This will minimize mistakes and increase efficiency.
Further, the integration of the two systems will aid in developing a multi-layered defense approach. IDs is able to offer visibility, whereas IPS is able to offer control. Thus, it provides monitoring and protection to the organizations. Several security solutions today have both features and can be configured to operate simultaneously in 2026. This tendency reveals the relevance of the combination of using them and not separately.
IDS vs IPS: Choosing the Right Solution for Your Network
Selecting between IDS and IPS depends on your specific requirements. Small businesses tend to be more attracted to IPS since it provides protection with automatic protection and few controls. Conversely, big businesses employ both systems to have greater control. Moreover, companies that have their own security services depend on IDS to provide them with a more in-depth analysis. They apply IPS to do policies and block threats in real-time. Thus, it will depend on the competence and the level of risk of your team.
Also, network size and complexity should be taken into consideration. Greater networks need enhanced solutions that involve monitoring and stopping. Group systems are therefore more feasible. Finally, the aim is to establish a balanced security arrangement that provides a view and security.
IDS vs IPS: Future Trends and Evolving Security Needs
Cyber threats are constantly increasing, and so is the IDS and IPS systems. Artificial intelligence is now used in tools to identify complex patterns. Hence, they will be able to detect threats that are not recognized by traditional systems. Moreover, there is an increase in the popularity of cloud-based security solutions. These systems offer scalability and flexibility to expand businesses. Due to this, businesses can make changes to their security strategies without difficulty.
Besides, the possibility of integration with other tools increases the protection in general. Now, IDS and IPS are operating with firewalls, endpoint security, and threat intelligence platforms. This provides an all around defense mechanism. Even more significantly in future, automation will be a part. There will be quicker responses of systems and less human involvement.
Conclusion: IDS vs IPS for Strong Network Protection
Comparison of IDS vs IPS illustrates the significance of detection and prevention towards network security. IDS offers visibility in the detection of suspicious activities, whereas IPS offers protection in real-time by blocking threats. That is why their combination will make a comprehensive and balanced security approach.
With threats that are constantly changing, organizations cannot afford to stick to simple protection measures. The integrated IDS and IPS solution provides awareness and control that intensifies security as a whole. These systems would enable businesses to secure their networks and remain prepared to take on future challenges by installing and maintaining them in the right way.
Also Read About :- Data Security Posture Management Tools for Modern